Antiracist economist Kim Crayton says that “intention with out technique is chaos.” We’ve mentioned how our biases, assumptions, and inattention towards marginalized and susceptible teams result in harmful and unethical tech—however what, particularly, do we have to do to repair it? The intention to make our tech safer just isn’t sufficient; we want a method.
Table of Contents:
- Design for Safety
- keyword installs services
- buy ios app downloads
- google play keyword research
This chapter will equip you with that plan of motion. It covers find out how to combine security rules into your design work with a view to create tech that’s protected, find out how to persuade your stakeholders that this work is critical, and the way to answer the critique that what we really want is extra range.
The method for inclusive security
If you find yourself designing for security, your objectives are to:
- determine methods your product can be utilized for abuse,
- design methods to stop the abuse, and
- present assist for susceptible customers to reclaim energy and management.
The Course of for Inclusive Security is a software that will help you attain these objectives . Whether or not you’re creating a wholly new product or including to an current characteristic, the Course of may also help you make your product protected and inclusive. The Course of consists of 5 normal areas of motion:
- Conducting analysis
- Creating archetypes
- Brainstorming issues
- Designing options
- Testing for security
Every facet of the Course of for Inclusive Security will be included into your design course of the place it makes essentially the most sense for you. The instances given are estimates that will help you incorporate the levels into your design plan.
The Course of is supposed to be versatile—it received’t make sense for groups to implement each step in some conditions. Use the elements which might be related to your distinctive work and context; that is meant to be one thing you may insert into your current design observe.
And as soon as you employ it, in case you have an thought for making it higher or just wish to present context of the way it helped your workforce. It’s a residing doc that I hope will proceed to be a helpful and real looking software that technologists can use of their day-to-day work.
If you happen to’re engaged on a product particularly for a susceptible group or survivors of some type of trauma, akin to an app for survivors of home violence, sexual assault, or drug habit, be sure you learn Chapter 7, which covers that scenario explicitly and must be dealt with a bit in another way. The rules listed below are for prioritizing security when designing a extra normal product that may have a large person base (which, we already know from statistics, will embrace sure teams that must be protected against hurt). Chapter 7 is concentrated on merchandise which might be particularly for susceptible teams and individuals who have skilled trauma.
STEP 1: CONDUCT RESEARCH
Design analysis ought to embrace a broad evaluation of how your tech could be weaponized for abuse in addition to particular insights into the experiences of survivors and perpetrators of that kind of abuse. At this stage, you and your workforce will examine problems with interpersonal hurt and abuse, and discover some other security, safety, or inclusivity points that could be a priority in your services or products, like knowledge safety, racist algorithms, and harassment.
Broad analysis
Your undertaking ought to start with broad, normal analysis into related merchandise and points round security and moral considerations which have already been reported. For instance, a workforce constructing a wise residence system would do nicely to know the multitude of ways in which current sensible residence gadgets have been used as instruments of abuse. In case your product will contain AI, search to know the potentials for racism and different points which were reported in current AI merchandise. Practically all varieties of know-how have some type of potential or precise hurt that’s been reported on within the information or written about by teachers. Google Scholar is a useful gizmo for locating these research.
Particular analysis: Survivors
When doable and applicable, embrace direct analysis (surveys and interviews) with people who find themselves specialists within the types of hurt you could have uncovered. Ideally, you’ll wish to interview advocates working within the area of your analysis first so that you’ve got a extra stable understanding of the subject and are higher geared up to not retraumatize survivors. If you happen to’ve uncovered doable home violence points, for instance, the specialists you’ll wish to converse with are survivors themselves, in addition to staff at home violence hotlines, shelters, different associated nonprofits, and attorneys.
Particularly when interviewing survivors of any type of trauma, you will need to pay individuals for his or her information and lived experiences. Don’t ask survivors to share their trauma at no cost, as that is exploitative. Whereas some survivors might not wish to be paid, you must at all times make the supply within the preliminary ask. A substitute for cost is to donate to a corporation working towards the kind of violence that the interviewee skilled. We’ll discuss extra about find out how to appropriately interview survivors in Chapter 6.
Particular analysis: Abusers
It’s unlikely that groups aiming to design for security will have the ability to interview self-proclaimed abusers or individuals who have damaged legal guidelines round issues like hacking. Don’t make this a purpose; relatively, attempt to get at this angle in your normal analysis. Goal to know how abusers or unhealthy actors weaponize know-how to make use of towards others, how they cowl their tracks, and the way they clarify or rationalize the abuse.
STEP 2: CREATE ARCHETYPES
When you’ve completed conducting your analysis, use your insights to create abuser and survivor archetypes. Archetypes aren’t personas, as they’re not primarily based on actual individuals that you just interviewed and surveyed. As an alternative, they’re primarily based in your analysis into possible questions of safety, very similar to once we design for accessibility: we don’t must have discovered a gaggle of blind or low-vision customers in our interview pool to create a design that’s inclusive of them. As an alternative, we base these designs on current analysis into what this group wants. Personas sometimes symbolize actual customers and embrace many particulars, whereas archetypes are broader and will be extra generalized.
The abuser archetype is somebody who will have a look at the product as a software to carry out hurt .They could be attempting to hurt somebody they don’t know via surveillance or nameless harassment, or they could be attempting to regulate, monitor, abuse, or torment somebody they know personally.
The survivor archetype is somebody who’s being abused with the product. There are numerous conditions to think about by way of the archetype’s understanding of the abuse and find out how to put an finish to it: Do they want proof of abuse they already suspect is going on, or are they unaware they’ve been focused within the first place and must be alerted (Fig 5.3)?
The survivor archetype Lisa Zwaan suspects her husband is weaponizing their residence’s IoT gadgets towards her, however within the face of his insistence that she merely doesn’t perceive find out how to use the merchandise, she’s not sure. She wants some type of proof of the abuse.
You could wish to make a number of survivor archetypes to seize a variety of various experiences. They could know that the abuse is going on however not have the ability to cease it, like when an abuser locks them out of IoT gadgets; or they realize it’s occurring however don’t know the way, akin to when a stalker retains determining their location (Fig 5.4). Embrace as many of those situations as you must in your survivor archetype. You’ll use these in a while if you design options to assist your survivor archetypes obtain their objectives of stopping and ending abuse.The survivor archetype Eric Mitchell is aware of he’s being stalked by his ex-boyfriend Rob however can’t determine how Rob is studying his location data.
It could be helpful so that you can create persona-like artifacts in your archetypes, such because the three examples proven. As an alternative of specializing in the demographic data we regularly see in personas, concentrate on their objectives. The objectives of the abuser shall be to hold out the precise abuse you’ve recognized, whereas the objectives of the survivor shall be to stop abuse, perceive that abuse is going on, make ongoing abuse cease, or regain management over the know-how that’s getting used for abuse. Later, you’ll brainstorm find out how to forestall the abuser’s objectives and help the survivor’s objectives.
And whereas the “abuser/survivor” mannequin suits most circumstances, it doesn’t match all, so modify it as you must. For instance, should you uncovered a problem with safety, akin to the power for somebody to hack into a house digicam system and discuss to youngsters, the malicious hacker would get the abuser archetype and the kid’s dad and mom would get survivor archetype.
STEP 3: BRAINSTORM PROBLEMS
After creating archetypes, brainstorm novel abuse circumstances and questions of safety. “Novel” means issues not present in your analysis; you’re attempting to determine utterly new questions of safety which might be distinctive to your services or products. The purpose with this step is to exhaust each effort of figuring out harms your product might trigger. You aren’t worrying about find out how to forestall the hurt but—that comes within the subsequent step.
How might your product be used for any type of abuse, outdoors of what you’ve already recognized in your analysis? I like to recommend setting apart at the least just a few hours together with your workforce for this course of.
If you happen to’re searching for someplace to begin, attempt doing a Black Mirror brainstorm. This train is predicated on the present Black Mirror, which options tales in regards to the darkish potentialities of know-how. Attempt to determine how your product could be utilized in an episode of the present—essentially the most wild, terrible, out-of-control methods it might be used for hurt. After I’ve led Black Mirror brainstorms, contributors normally find yourself having a great deal of enjoyable . I like to recommend time-boxing a Black Mirror brainstorm to half an hour, after which dialing it again and utilizing the remainder of the time considering of extra real looking types of hurt.
After you’ve recognized as many alternatives for abuse as doable, you should still not really feel assured that you just’ve uncovered each potential type of hurt. A wholesome quantity of hysteria is regular if you’re doing this type of work. It’s widespread for groups designing for security to fret, “Have we actually recognized each doable hurt? What if we’ve missed one thing?” If you happen to’ve spent at the least 4 hours developing with methods your product might be used for hurt and have run out of concepts, go to the following step.
It’s unimaginable to ensure you’ve considered every part; as an alternative of aiming for 100% assurance, acknowledge that you just’ve taken this time and have carried out the perfect you may, and decide to persevering with to prioritize security sooner or later. As soon as your product is launched, your customers might determine new points that you just missed; purpose to obtain that suggestions graciously and course-correct rapidly.
STEP 4: DESIGN SOLUTIONS
At this level, you must have an inventory of the way your product can be utilized for hurt in addition to survivor and abuser archetypes describing opposing person objectives. The subsequent step is to determine methods to design towards the recognized abuser’s objectives and to assist the survivor’s objectives. This step is an efficient one to insert alongside current elements of your design course of the place you’re proposing options for the assorted issues your analysis uncovered.
Some inquiries to ask your self to assist forestall hurt and assist your archetypes embrace:
- Are you able to design your product in such a approach that the recognized hurt can’t occur within the first place? If not, what roadblocks can you set as much as forestall the hurt from occurring?
- How will you make the sufferer conscious that abuse is going on via your product?
- How will you assist the sufferer perceive what they should do to make the issue cease?
- Are you able to determine any varieties of person exercise that might point out some type of hurt or abuse? Might your product assist the person entry assist?
In some merchandise, it’s doable to proactively acknowledge that hurt is going on. For instance, a being pregnant app could be modified to permit the person to report that they had been the sufferer of an assault, which might set off a suggestion to obtain assets for native and nationwide organizations. This type of proactiveness just isn’t at all times doable, but it surely’s value taking a half hour to debate if any kind of person exercise would point out some type of hurt or abuse, and the way your product might help the person in receiving assist in a protected method.
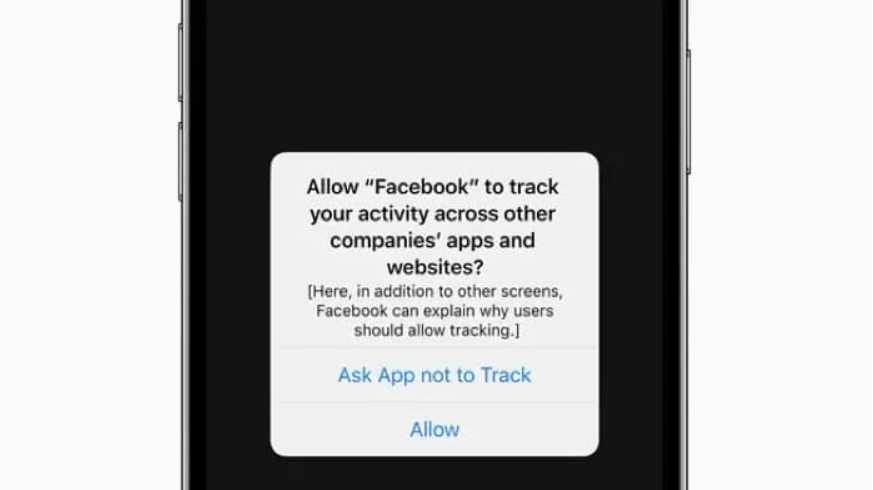
That stated, use warning: you don’t wish to do something that might put a person in hurt’s approach if their gadgets are being monitored. If you happen to do supply some type of proactive assist, at all times make it voluntary, and assume via different questions of safety, akin to the necessity to preserve the person in-app in case an abuser is checking their search historical past. We’ll stroll via a very good instance of this within the subsequent chapter.
STEP 5: TEST FOR SAFETY
The ultimate step is to check your prototypes from the perspective of your archetypes: the one who desires to weaponize the product for hurt and the sufferer of the hurt who must regain management over the know-how. Identical to some other type of product testing, at this level you’ll purpose to carefully take a look at out your security options so as to determine gaps and proper them, validate that your designs will assist preserve your customers protected, and really feel extra assured releasing your product into the world.
Ideally, security testing occurs together with usability testing. If you happen to’re at an organization that doesn’t do usability testing, you would possibly have the ability to use security testing to cleverly carry out each; a person who goes via your design making an attempt to weaponize the product towards another person can be inspired to level out interactions or different parts of the design that don’t make sense to them.
You’ll wish to conduct security testing on both your last prototype or the precise product if it’s already been launched. There’s nothing unsuitable with testing an current product that wasn’t designed with security objectives in thoughts from the onset—“retrofitting” it for security is an efficient factor to do.
Do not forget that testing for security entails testing from the angle of each an abuser and a survivor, although it could not make sense so that you can do each. Alternatively, should you made a number of survivor archetypes to seize a number of situations, you’ll wish to take a look at from the angle of every one.
As with different types of usability testing, you because the designer are most definitely too near the product and its design by this level to be a useful tester; you already know the product too nicely. As an alternative of doing it your self, arrange testing as you’d with different usability testing: discover somebody who just isn’t accustomed to the product and its design, set the scene, give them a job, encourage them to assume out loud, and observe how they try to finish it.
Abuser testing
The purpose of this testing is to know how straightforward it’s for somebody to weaponize your product for hurt. In contrast to with usability testing, you need to make it unimaginable, or at the least troublesome, for them to attain their purpose. Reference the objectives within the abuser archetype you created earlier, and use your product in an try to attain them.
For instance, for a health app with GPS-enabled location options, we will think about that the abuser archetype would have the purpose of determining the place his ex-girlfriend now lives. With this purpose in thoughts, you’d attempt every part doable to determine the situation of one other person who has their privateness settings enabled. You would possibly attempt to see her operating routes, view any obtainable data on her profile, view something obtainable about her location (which she has set to non-public), and examine the profiles of some other customers in some way related along with her account, akin to her followers.
If by the tip of this you’ve managed to uncover a few of her location knowledge, regardless of her having set her profile to non-public, you already know now that your product allows stalking. The next step is to return to step 4 and determine find out how to forestall this from occurring. You could must repeat the method of designing options and testing them greater than as soon as.
Survivor testing
Survivor testing entails figuring out find out how to give data and energy to the survivor. It won’t at all times make sense primarily based on the product or context. Thwarting the try of an abuser archetype to stalk somebody additionally satisfies the purpose of the survivor archetype to not be stalked, so separate testing wouldn’t be wanted from the survivor’s perspective.
Nonetheless, there are circumstances the place it is smart. For instance, for a wise thermostat, a survivor archetype’s objectives could be to know who or what’s making the temperature change after they aren’t doing it themselves. You would take a look at this by searching for the thermostat’s historical past log and checking for usernames, actions, and instances; should you couldn’t discover that data, you’d have extra work to do in step 4.
One other purpose could be regaining management of the thermostat as soon as the survivor realizes the abuser is remotely altering its settings. Your take a look at would contain making an attempt to determine how to do that: are there directions that specify find out how to take away one other person and alter the password, and are they straightforward to seek out? This would possibly once more reveal that extra work is required to make it clear to the person how they’ll regain management of the system or account.
Stress testing
To make your product extra inclusive and compassionate, think about including stress testing. This idea comes from Design for Actual Life by Eric Meyer and Sara Wachter-Boettcher. The authors identified that personas sometimes heart people who find themselves having a very good day—however actual customers are sometimes anxious, stressed, having a foul day, and even experiencing tragedy. These are known as “stress circumstances,” and testing your merchandise for customers in stress-case conditions may also help you determine locations the place your design lacks compassion. Design for Actual Life has extra particulars about what it seems to be like to include stress circumstances into your design in addition to many different nice ways for compassionate design.